Security automation is critical to identifying threats and resolving alerts faster. It plays a starring role in the latest release of our cloud-native Security Orchestration and Automation (SOAR) platform, ActiveEye 2.0.
Here are just a few highlights of all the new features:
- Advanced security automation processes more than 95 percent of alerts, so our security operations center (SOC) analysts can focus on the most complex and critical alerts and take that load off your in-house team.
- Personalized Customer Notebooks offer the option to leave messages for our SOC team about what’s important or what to ignore, such as employees on international travel or internal system testing exercises.
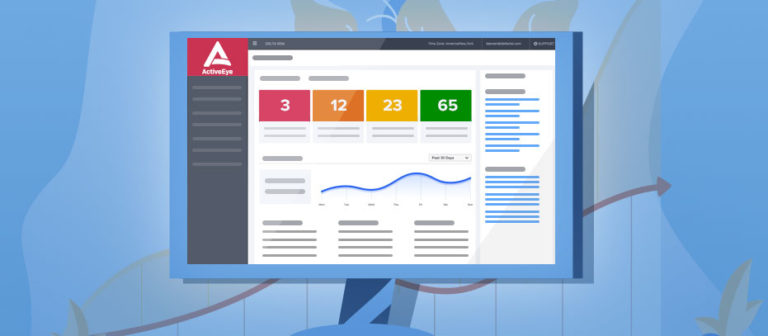
- Alert Resolution Metrics dashboards make it easy to see what’s happening across your entire environment and create executive reports. You can also see Key Performance Indicators (KPIs) such as how long it takes for alerts to be resolved.
Endpoints, network security information and event management (SIEM), cloud applications, and cloud infrastructure generate thousands of alerts daily. With ActiveEye 2.0, you can view and manage them all or have our SOC analysts manage them. Let’s take a more detailed look now at each of the features and how they use security automation.
Watch our short video overview now to learn more.
Virtual Analyst Playbook Orchestration
One of the most important features in ActiveEye 2.0 is our Virtual Analyst Playbook Orchestration. Dynamic data from threat intelligence sources and other events is applied at scale to millions of alerts via a “virtual analyst.” This enables us to automatically process more than 95 percent of incoming alerts.
Removing most of the false positives creates more time for actual threat hunting and investigating complex threats. Playbooks reduce the human analyst’s manual workload by an average of 90 percent. They can automatically pull in threat intelligence from VirusTotal or IBM X-Force Exchange, DNS data from Neustar, and other data fields in alerts. They can even look at historical trends for users or systems.
Many alerts can be addressed or closed without human intervention or review. Once the virtual analyst eliminates all the noise, human analysts can begin to investigate the remaining security cases. As they do, they can see all historical information about an alert, user, or system gathered by the virtual analyst and displayed in the platform. They can also see previous alerts of a similar nature, any work that other analysts have already done, and any input from clients.
Analysts can also access raw event data from on-premise security monitoring devices (like intrusion detection) and networks (via your SIEM). We can include data from cloud applications and infrastructure, too. This gives analysts even more context as needed and further speeds response times.
In addition to the global rules for known alerts, you can also create custom rules at a company level. For example, you could add a rule such as “check for multifactor authentication” or “check the whitelist.”
Virtual Analyst Prioritization
The Virtual Analyst Prioritization feature uses machine learning to get smarter over time based on previous classifications of similar alerts. This is yet another means to enable a human analyst to focus on the activity most likely to require a response. If the Virtual Analyst can determine a likely response, it will recommend it to the analyst.
Virtual Analyst Response Automation
This feature allows analysts to take action directly from the ActiveEye platform, which also dramatically improves response times. For example, if an analyst is dealing with an endpoint security event, they can initiate a response immediately. This could include removing a file, blacklisting or whitelisting the file, or initiating a scan.
Analysts can take action with a click of a button within ActiveEye. This eliminates the need to log into a separate endpoint security portal, saving valuable time.
Alert Resolution Metrics
Another focus area in ActiveEye 2.0 is improved transparency and simplifying co-managed security. As a result, you can now view and manage Key Performance Indicators (KPIs) and Alert Resolution Times jointly with our SOC analysts.
With ActiveEye, we track how long it takes from when every alert is created to when it is resolved. You can see those metrics in your personalized dashboard to spot any anomalies and see trends over time. The dashboard makes it easy to share this information with your executive management team in a convenient, easy-to-understand format.
Customer Notebook
The Customer Notebook helps SOC analysts get the information they need 24×7 to properly evaluate and escalate security cases faster. You can post notes to let our SOC analysts know what’s more urgent or what they can safely ignore. For example, you may be running system tests or have an employee who is traveling internationally. This might trigger a lot of alerts that don’t require any action or notification.
Our security team can see whatever is in your notebook, along with escalation procedures, case history, and other key data, while they’re investigating activity. This helps them focus on engaging you faster and eliminates unnecessary and annoying communications.
Customized Investigation and Reporting
Another feature in ActiveEye 2.0 allows you to customize Investigation and Reporting data from within the platform. You can apply complex filtering and create customized column views, save and share information with others, and download it in a raw data or summarized format.
Summary
We appreciate all the input we’ve had from our customers on the features in the ActiveEye 2.0 release. If you’d like to learn more, we invite you to get a demo of ActiveEye 2.0. See how you can get advanced threat detection, expert investigation, and rapid response at a fraction of the cost of building your own SOC.