Managed Security Services
Delta Risk is now part of Motorola Solutions
For the latest updates about our technologies and Motorola Solutions’ cybersecurity offerings, visit Motorola Solutions.
A Comprehensive Cyber Security Solution
Where Are You in Your Security Journey?
Is your current SIEM creating more work and less value?
Feel Confident and Gain Clarity into Your Security Alerts and Existing SIEM
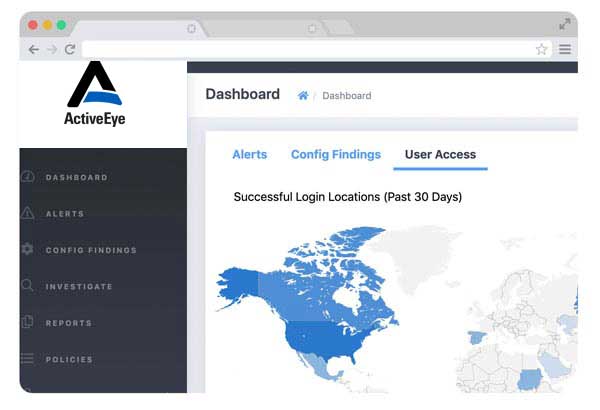
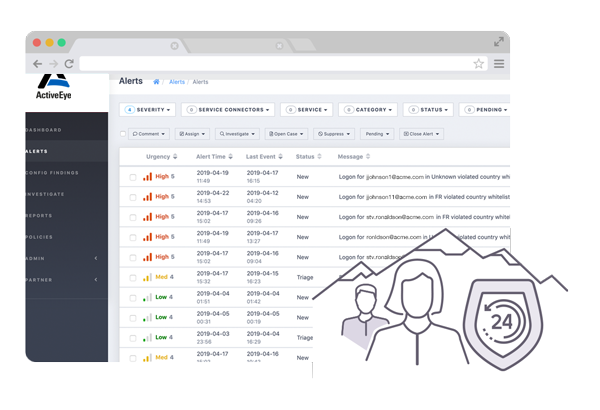
ActiveEye integrates with the security tools you already use, enabling you to optimize and scale Managed Detection and Response (MDR) capabilities across your organization. It eliminates the noise, allowing you to focus on the tasks that need your attention. With automation and pre-packaged policies, you can resolve critical threats faster. The ActiveEye platform powers the Delta Risk Managed Security services.
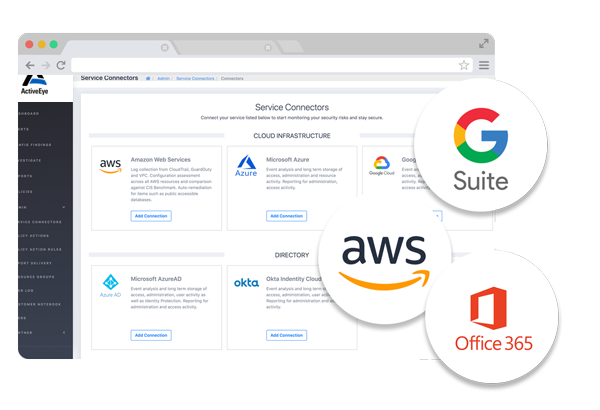
Is your business moving to the cloud and leaving security behind?
Bridge the Gap to a Secure Hybrid and Cloud Environment
Cloud service providers deliver strong platforms, but it’s up to each organization using them to configure networking, access controls, and monitoring in a secure fashion. Since configuring cloud environments like Amazon Web Services (AWS), Microsoft Azure, and Google is new to most organizations, many lack the experience to get it right the first time. Mistakes can be costly, resulting in cloud data breaches and security incidents. Even if your organization is “just experimenting” with cloud platforms and services, you can be at risk
Are you having trouble staffing all of your security projects?
Gain an Understanding of Your Current Risks and Build a Solid Defense
Testing your technology to discover cyber security gaps is only part of the solution. You also need to test your people and processes to properly secure your network, endpoints, and applications. Delta Risk offers a comprehensive suite of professional services, delivered by security experts, to close possible attack vectors. If cyber criminals have already broken through your defenses, we can help you quickly contain incidents and get your business back on track.
Is the cost of building your own 24×7 security coverage out of reach?
Increase Protection and Enhance Your Security with Our SOC-as-a-Service
The ActiveEye team continuously monitors your systems and data – both inside and outside your company network – to detect and respond to threats. Our group of trained, experienced, US-based analysts provides actionable recommendations and produces real results by preventing incidents and minimizing damage, all for far less than the cost of building your own 24×7 SOC.
SaaS Applications | Cloud InfrastructureNetwork | Network | Endpoint
An Extensive Solution for Our Security Partners
Are your customers looking to you for cyber security consulting and information security services? By partnering with Delta Risk, you can quickly expand your service offerings without the expense and time it takes to develop solutions in house or hire new employees. Take advantage of our expertise and reduce your costs while providing a better customer experience with our managed security solutions and security consulting services.
Technology

Increase Value
Give your customers added value though plug-and-play security solutions in addition to your current offerings.
Process

Recurring Revenue
Managed security solutions provide a subscription-based business model for a steady revenue stream.
People
Fully Branded
With the ability to white label the reporting and user experience, you can provide a seamless solution.

SOC 2 Compliant
System and Organization Controls 2 (SOC 2) is a comprehensive audit that focuses on system-level controls of a service organization which focuses on the protection and privacy of data. Delta Risk has achieved SOC 2 compliance through an extensive review process. While SOC 2 compliance isn’t a requirement for SaaS and cloud computing vendors, we feel it is an essential component in establishing your trust as a security partner.